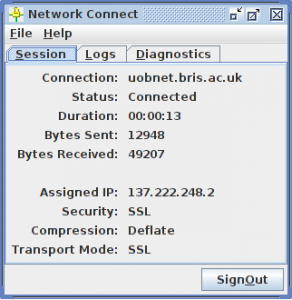
In September 2013 IT Services launched a new VPN service, based around Junos Pulse. This replaced the older PPTP based service, but the two ran in parallel for 9 months to give people a chance to transition.
On 30th June 2014 08:45, the PPTP VPN was switched off, ending 12 years of PPTP VPN use at the University of Bristol.
The story starts not with a VPN, but with wireless networking…
In 2001, Bristol dipped its toe into wireless networking, and started work on the “Nomadic Network”
Wireless technology was still young, and wireless encryption wasn’t widely supported on client devices. So Nomadic used an open, unencrypted SSID with restricted routing. The only thing you could get to was a bank of PPTP VPN concentrators, referred to as “roamnodes”
These roamnodes were cheap commodity x86 boxes with no disk. They booted a custom linux live CD which held its config on a floppy disk. This made upgrades/rollback really easy (pull out the CD, put the new one in, reverse process to revert)
The idea was that you connected to the wireless (or plugged your laptop in to one of the public network sockets, and connected to the access network via PPPoE), then span up a VPN connection to get on the university network.
That all sounds a bit clunky these days, but back then it was sophisticated enough that several other universities around the UK picked up the system – and we won the UCISA Award for Excellence in 2003. (Which caused a certain amount of amusement in the office at the time. They managed to misspell “Excellence” on the oversized novelty presentation cheque!)
As a VPN was an integral part of the Nomadic Network, it was convenient to use the same technology to provide off-site access to UoB restricted resources (as anyone using the wireless already had the client configured)
By 2005 wireless technology had moved on and work started to replace the Nomadic Network with a wireless system which eventually evolved into the eduroam service we have today.
Although the wireless no-longer had need of a VPN component, the VPN was retained and rebuilt as a stand alone service. The service had a refresh in 2007 to upgrade it to CentOS 5 – and it’s been running the same OS, on the same hardware ever since.
That hardware is long since out of extended hardware maintenance (and both of the remaining nodes have known hardware issues) client support for PPTP is now patchy and difficult to debug, it’s not compatible with a lot of home broadband routers, some major ISPs actively block PPTP and finally, the encryption used in our implementation had some weaknesses which we’d really rather it hadn’t! (although we have no evidence that those weaknesses were ever exploited)
So that’s why we’ve replaced it!
In some ways, I’m sorry to see it go as it’s one of the services I was initially employed to support. In many other ways though, it’s done its job and been surpassed by other technology. Maintenance and support of the service had become problematic. It’s time to move on.
For a service with approximately 500 users a month, it needed a surprising number of resources to keep it going.
Now that it’s gone we can shut down 2 physical PPTP head nodes, 5 unmanaged virtual linux servers which provide supporting services (authentication, dhcp, dns, web redirects etc) and 2 hypervisors which are also out of hardware maintenance.
The new Junos Pulse VPN is a single appliance. Much more efficient on rack space, power and cooling!